Enabling Secure and Seamless User Authentication with VoIP
In an era dominated by Voice over Internet Protocol (VoIP) communication, ensuring the security of our conversations has become paramount. As businesses and individuals increasingly rely on VoIP for their daily communication needs, the significance of robust user authentication cannot be overstated.
User authentication acts as the digital gatekeeper, allowing only authorized individuals to access the network and engage in phone calls.

What is User Authentication?
User authentication is a foundational safeguard in VoIP technology, ensuring that only authorized individuals gain access to the network and the privilege of making or receiving calls. User authentication serves as a digital lock and key mechanism, requiring users to validate their identity through distinct credentials before participating in VoIP communications.
At its core, user authentication refers to the process of verifying the legitimacy of users attempting to connect to a VoIP network. This verification entails a combination of factors such as a unique user name, a confidential password, or even the association with a pre-approved device. Each of these facets constitutes a layer of security, collectively mitigating the risk of unauthorized access and fraudulent activity.
The significance of user authentication extends beyond mere protection; it reinforces the concept of privacy and trust in VoIP communications. By confirming the authenticity of users, businesses, and individuals can engage in conversations, confident that their sensitive information remains shielded from potential eavesdroppers and cyber threats.
User authentication is particularly crucial in VoIP environments due to the digital nature of these communications. Unlike traditional telephony, VoIP traverses the vast expanse of the internet, making it susceptible to new security vulnerabilities. Without stringent authentication measures, malicious actors could exploit these vulnerabilities to infiltrate conversations, compromise data integrity, or perpetrate identity theft.
The Business Imperative for User Authentication
Businesses operate in an environment where competitive advantage hinges on information confidentiality, customer trust, and regulatory compliance. In this context, user authentication is a formidable shield against potential breaches. By implementing stringent authentication mechanisms, businesses can ensure that only authorized personnel gain access to VoIP networks, mitigating the risks of unauthorized interception and data compromise.
Furthermore, the increasing prevalence of remote work and bring-your-own-device (BYOD) policies amplifies the need for fortified authentication. With employees connecting from diverse locations and devices, the potential attack surface for cybercriminals widens.
The business case for user authentication in VoIP extends to compliance obligations. Many industries are subject to stringent data protection regulations, mandating organizations to secure communications containing sensitive customer information. Failure to comply exposes businesses to legal repercussions and erodes customer trust.
User authentication is not merely an optional feature but an integral element of VoIP for businesses. By prioritizing security, organizations can foster a climate of trust, protect proprietary data, and adhere to regulatory mandates. So, how can you facilitate user authentication in your phone systems?
Facilitating User Authentication in VoIP
Single Sign-On (SSO)
In the intricate world of VoIP security, where streamlined communication and impregnable safeguards are paramount, the Single Sign-On (SSO) method is a game-changing solution. SSO represents a paradigm shift in user authentication, simplifying access without compromising security.
SSO addresses the common challenge of managing multiple usernames and passwords across different platforms. In the context of VoIP, it allows users to access the network and initiate calls using a single set of credentials. This not only enhances the user experience but also minimizes the risk of weak passwords due to password fatigue.
By integrating SSO with VoIP, businesses can seamlessly extend their existing authentication systems to VoIP communication channels. Employees can effortlessly move from their workstations to VoIP calls without the hassle of repeated logins. This enhanced convenience encourages widespread adoption, minimizing the chances of users circumventing security measures due to usability constraints.
Additionally, SSO bolsters security by centralizing user authentication. The authentication process occurs within a secure and controlled environment, reducing the potential attack vectors that arise from authentication taking place across disparate systems. Businesses can implement granular access controls, ensuring that only authorized personnel gain entry to VoIP networks.
Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) is a robust defense against unauthorized access in VoIP security, where protecting sensitive conversations and data is paramount. MFA introduces an additional layer of security by requiring users to provide multiple forms of verification before gaining entry to VoIP networks.
MFA goes beyond the traditional reliance on a single password. It encompasses a combination of factors such as something the user knows (password) and something the user has (a mobile device or security token). This multi-pronged approach significantly enhances security by making it exceedingly difficult for attackers to compromise all the required factors.
For businesses, MFA in VoIP provides an invaluable shield against potential breaches. Even if a password is compromised through phishing or other means, unauthorized access is thwarted by the need for additional authentication elements. This is particularly crucial when sensitive customer data or confidential business discussions are transmitted over VoIP channels.
While MFA unquestionably augments security, balancing its benefits with user experience is essential. Striking this equilibrium involves selecting appropriate authentication factors and ensuring that the verification process remains streamlined.
STIR/SHAKEN
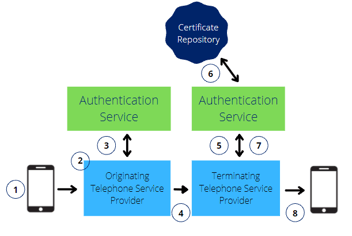
The STIR (Secure Telephone Identity Revisited) and SHAKEN (Signature-based Handling of Asserted information using toKENs) framework is a formidable solution to combat caller ID spoofing and enhance caller authentication.
Caller ID spoofing, a technique malicious entities use to manipulate incoming call information, undermines the trustworthiness of VoIP communication. The STIR/SHAKEN framework addresses this concern by validating the authenticity of calling parties. STIR involves the authentication of caller identities, while SHAKEN employs cryptographic signatures to attest to the accuracy of call information.
This framework operates as a trust mechanism, where originating service providers digitally sign call details, and the receiving service providers verify these signatures. This process validates the caller's legitimacy and confirms that the call data hasn't been tampered with during transit.
For businesses, STIR/SHAKEN is a critical tool in maintaining the integrity of their communications. It ensures that the recipient can trust the identity displayed on the caller ID, reducing the risk of falling victim to scams or fraudulent calls.
However, the successful implementation of STIR/SHAKEN requires widespread industry adoption and collaboration. Service providers must work collectively to establish a secure network of authentication and verification, thereby creating a robust shield against caller ID manipulation.
Elevating VoIP Communication Through Secure Authentication
As businesses and individuals navigate the digital landscape, understanding and implementing advanced authentication methods like SSO, MFA, and the STIR/SHAKEN framework becomes imperative.
These innovations fortify data protection and amplify user experience, building trust and reliability in every call. At SimplicityVoIP, we are committed to VoIP security, offering robust authentication solutions to ensure a safe communication environment.